
Cloud Storage in WideBand High-Security Data Centers
Much has been said about the advantages of moving to a cloud-based architecture but security remains the number one concern among data managers. The KryptoVault data storage service provides a hardware-encrypted alternative to traditional cloud providers. Because data is AES-256 encrypted by a GoldKey Token before leaving the user’s device, the data is transmitted and stored in a form that not even WideBand personnel can read.

- Add storage at any time without tossing previous investment
- Multi-factor authentication with GoldKey Tokens
- Share files and tailor access permissions for each user
- Improve flexibility and efficiency with central management of users and vaults
- Protect confidential files with AES-256 encryption
Hardware-based Encryption
KryptoVault storage is accessed exclusively using GoldKey Tokens for multi-factor authentication, end-to-end symmetric encryption, and hardware-based key management. This level of security means that even if an attacker were able to obtain root access to any server or device in WideBand data centers, they would be unable to read customer vaults without that customer’s token. Other solutions do not offer customer-controlled, military-grade data encryption or rely on less secure software-only security.
More about GoldKey Technology
Easy to Use
Users can open and drag-and-drop files in KryptoVault much like a flash drive. The files are automatically encrypted and decrypted seamlessly to the user. Shortcuts to files or folders in a vault can be placed on user Desktops or emailed to a co-worker. No username is required since the user is recognized based on what token they use. They need only enter their password. This helps to ease the user experience and reduce training and support requirements.
High Availability and Triple Redundant
KryptoVault data is stored in multiple WideBand high-security data centers with three copies of the encrypted data automatically maintained to protect against hardware failures and catastrophic events that would lead to data loss or downtime. The internal network and server hardware is manufactured by WideBand and maintained 24×7 by experienced WideBand engineers. WideBand’s primary data center is located underground for extra protection against outside elements. More about WideBand Data Centers
Massively Scalable
KryptoVault storage can be scaled from 10 gigabytes to many terabytes. Professional vaults are also available with 1 Gigabit and 10 Gigabit connectivity options for ultra-low latency and high performance access. KryptoVault users can have peace of mind knowing that their vaults can grow as needed.
Server Replacement:
- Storage is automatically backed up and redundant with 24×7 support personnel
- Capacity can be increased as needed without power, cooling, or other facility concerns
- Users automatically see all their vaults without memorizing server names
- GoldKey encryption and authentication provide greater security than most local servers
- Vaults can be securely accessed from anywhere without VPN requirements
Private Connectivity Replacement:
- Strong encryption provides inherent security against insider attacks
- Secure access is available to mobile users
- Built-in access management and logs provide granular control and oversight
- Standard Internet connectivity can be used to provide a potential cost savings
How to Use KryptoVault: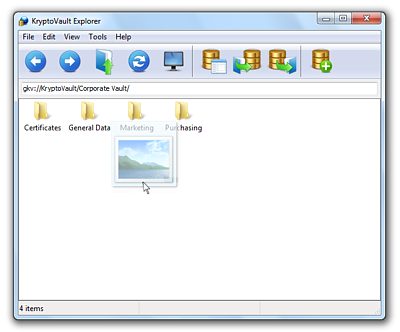
1) Insert GoldKey Token into USB Port and enter correct password
2) Drag-and-drop files to and from the vaults as needed
3) Remove GoldKey Token to lock the vaults automatically
Hierarchical AES Key Management:

GoldKey uses a three-tier Hierarchical AES Key Management System to give organizations a simple, yet powerful, way to distribute trust, manage authority and monitor access.
Learn more about Key Management
Select a KryptoVault option that fits the overall storage and performance needs of your whole organization. Once your Master KryptoVault has been associated with your organization’s GoldKey hierarchy, you will be able to assign individual vaults for various GoldKey Tokens or GoldKey groups in your organization.
KryptoVault
Shared Encrypted StorageRequest a Quote
